
Summit Hosting was proud to continue its sponsorship and present at the 2021 Vrakas Blum Computer Consulting (VBCC) Sage 100 User Group Meeting on Wednesday, October 20, 2021. This three-day virtual conference focused on the continuing education of Sage Software users on a variety of topics, including
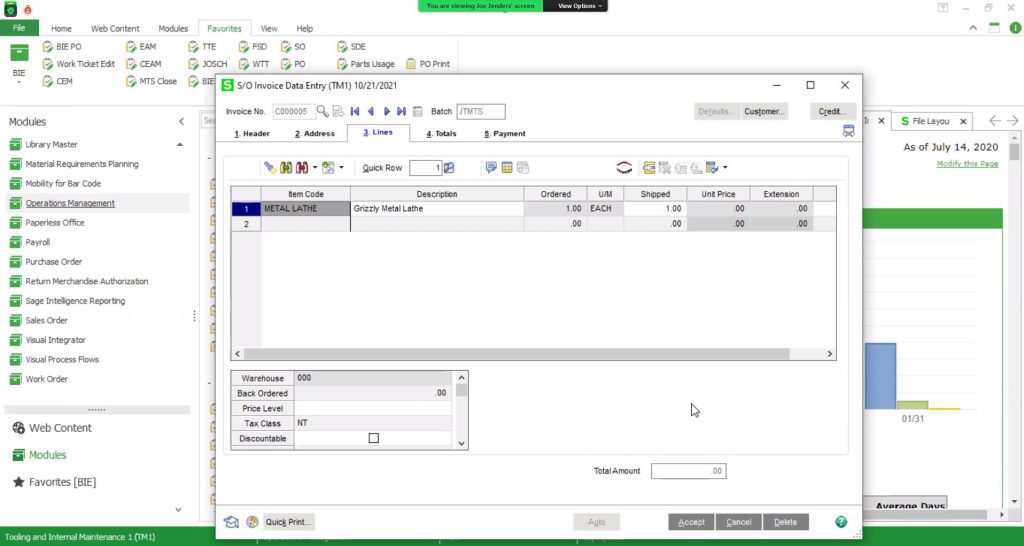
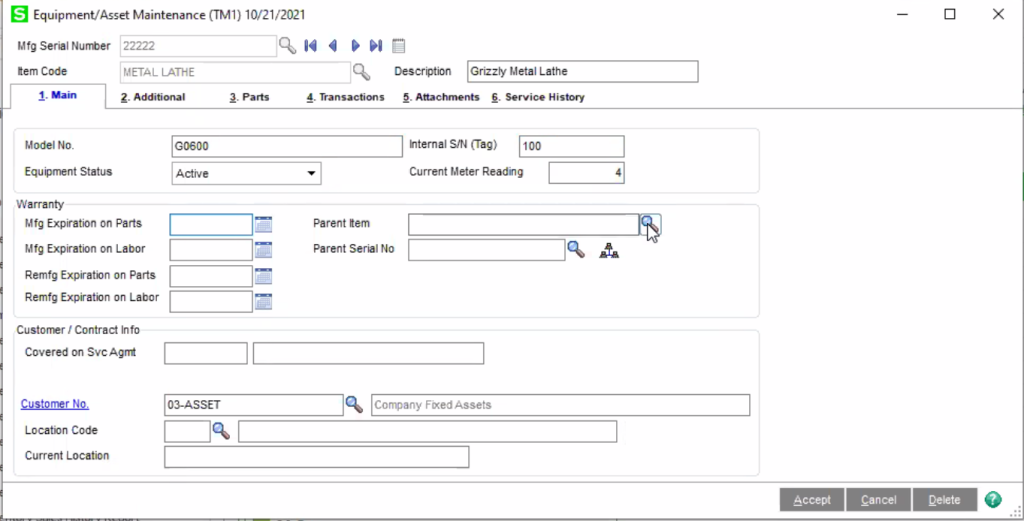
- Core Sage 100 functionality
- Warehouse and Multi-Bin Functionality
- Manufacturing Scanning and Sage Operations Management
As a Diamond Partner and Sage's #1 Manufacturing Solutions Provider, VBCC presented the latest features in operations management, including how assets can be created through manufacturing operations.
Although many manufacturers were initially hesitant to adopt cloud technology, manufacturing has changed from when all work was performed in a single giant factory, and adoption is now increasing quickly. With manufacturer's sales representatives on the road, many engineering and administrative functions becoming remote and more complex supply chains, many companies have adopted the cloud to adapt and innovate. Combining these structural changes with the massive increase in data and a workforce that grew up with the internet, cloud computing is a natural progression, and Sage 100 works excellent in the cloud!
With more connected cloud services, and the massive increase in cyberattacks, the need to increase cyber security is becoming a top priority.

Cyberattack prevention requires vigilance from the entire organization as well as the IT department or cloud service provider. Prevention strategies are top to bottom, starting with executive leadership down to awareness training for employees. Some guidelines for prevention include:
Be careful what you click.
- Links or attachments in emails you weren’t expecting to receive are often malicious.
Perform regular scans.
- Malware can travel from your computer over a network to others’ computers or your server.
Use strong passwords.
- Use different passwords for every account when possible and the longer you make them the better.
- Password vault applications are your best friend!
Advanced Tools.
- Artificial intelligence agents deployed inside the network can find patterns used by hackers to stop activity before it causes damage.
- Training and testing tools for your staff include awareness and fake attacks to see how users react.
- Periodic external intrusion testing can point out weaknesses in your perimeter defenses.
The future of business is in an always on, always secure, available from anywhere cloud. Contact us today to learn more about how Summit Hosting can secure your Sage 100 system with dedicated cloud servers and keep your business ready for the future.
